Rijndael Cipher | Vibepedia
The Rijndael cipher is a symmetric-key block cipher. It offers robust security with varying key lengths of 128, 192, and 256 bits, all operating on a fixed…
Contents
Overview
The story of the Rijndael cipher begins in the mid-1990s, a period when the world was grappling with the impending expiration of the Data Encryption Standard (DES) and the need for a more secure, modern encryption algorithm. In 1997, NIST initiated a public competition to find a successor. The winning submission, Rijndael, was the product of a collaboration between Joan Daemen, then working at Katholieke Universiteit Leuven, and Vincent Rijmen, an independent researcher. Their design, named after themselves, was chosen due to its strong security, efficiency, and flexibility. NIST officially adopted it as the Advanced Encryption Standard (AES) in FIPS PUB 197, published on November 26, 2001, marking a significant milestone in global data security.
⚙️ How It Works
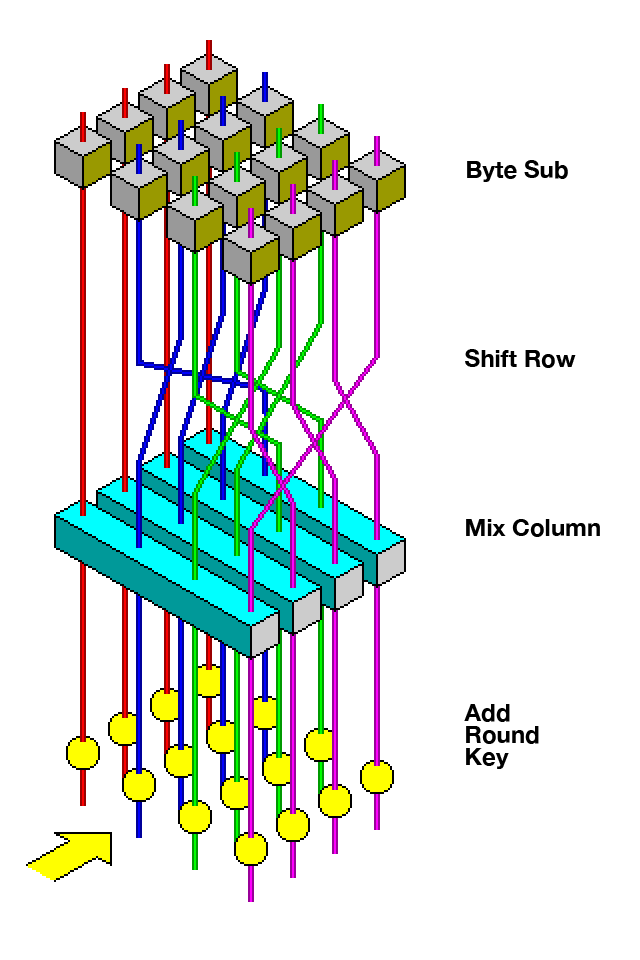
At its heart, the Rijndael cipher is a substitution-permutation network that operates on fixed-size blocks of data, typically 128 bits for AES. The encryption process involves multiple rounds, with the number of rounds dependent on the key length: 10 rounds for 128-bit keys, 12 for 192-bit keys, and 14 for 256-bit keys. Each round consists of four distinct transformations: a SubBytes step (a non-linear substitution using a fixed S-box), a ShiftRows step (a linear byte-wise permutation), a MixColumns step (a linear mixing operation within columns), and an AddRoundKey step (a bitwise XOR with a round key derived from the main cipher key). The final round omits the MixColumns step. Decryption is the inverse of this process, using inverse transformations.
📊 Key Facts & Numbers
The Rijndael cipher, as standardized in AES, supports three key lengths: 128, 192, and 256 bits, all operating on 128-bit blocks. This means a 128-bit key requires 10 rounds of encryption, a 192-bit key requires 12 rounds, and a 256-bit key demands 14 rounds. The total number of possible keys for AES-128 is 2^128, a number so astronomically large that brute-force attacks are considered computationally infeasible with current technology. For comparison, the older DES had only 2^56 possible keys, making it vulnerable to modern computing power. The AES standard has been adopted by over 90% of all cryptographic algorithms used today, according to some industry estimates.
👥 Key People & Organizations
The architects of the Rijndael cipher are Joan Daemen and Vincent Rijmen, two Belgian cryptographers whose innovative design won the NIST competition. Their work propelled them to international recognition in the field of cryptography. The NIST played a pivotal role in selecting and standardizing the algorithm, ensuring its global adoption and trustworthiness. Other key organizations involved in the AES process included various government agencies and academic institutions that participated in the rigorous evaluation of submitted algorithms, ensuring a thorough and transparent selection.
🌍 Cultural Impact & Influence
The Rijndael cipher's influence extends far beyond its technical specifications; it has become a cornerstone of digital trust and security worldwide. Its adoption as AES by the US government and subsequently by international bodies has made it the de facto standard for securing sensitive data. This ubiquity means that billions of devices, from smartphones and laptops to servers and IoT devices, rely on Rijndael's principles daily. Its elegant design has also inspired countless academic papers and further research in symmetric-key cryptography, solidifying its legacy in the field.
⚡ Current State & Latest Developments
As of 2024, the Rijndael cipher, primarily through its AES implementation, remains the dominant symmetric encryption algorithm globally. While no practical cryptographic breaks have been found against AES with standard key sizes, research continues into potential side-channel attacks and theoretical vulnerabilities. Hardware implementations of AES are now ubiquitous, integrated into CPUs by manufacturers like Intel and ARM, offering highly efficient encryption and decryption capabilities. The ongoing development of quantum computing, however, presents a long-term theoretical threat to current cryptographic standards, including AES, prompting research into post-quantum cryptography.
🤔 Controversies & Debates
Despite its widespread acceptance and rigorous vetting, the Rijndael cipher has not been entirely free from scrutiny. Early concerns, particularly during the NIST selection process, revolved around the potential for backdoors or weaknesses introduced by government agencies, a fear amplified by revelations like Project PRISM. While extensive cryptanalysis has failed to uncover any practical flaws in the core algorithm itself, discussions persist regarding implementation vulnerabilities and the security of key management practices. Some theoretical attacks, though not practically feasible against standard AES, continue to be explored by researchers.
🔮 Future Outlook & Predictions
The future of the Rijndael cipher is intrinsically linked to the evolution of computing and cryptography. While AES is expected to remain secure against classical computers for the foreseeable future, the advent of large-scale quantum computers poses a significant long-term threat. Cryptographers are actively developing post-quantum cryptographic algorithms that are resistant to quantum attacks. However, the transition to new standards will be a complex and lengthy process. It's plausible that Rijndael, or variants thereof, will continue to be used in hybrid systems or for applications where quantum threats are not yet a primary concern, potentially for decades to come.
💡 Practical Applications
The practical applications of the Rijndael cipher are vast and pervasive, underpinning much of modern digital security. It is used to encrypt data at rest, such as files stored on hard drives (e.g., BitLocker and APFS) and databases. It also secures data in transit, powering TLS/SSL connections for secure web browsing (HTTPS), virtual private networks (VPNs), and secure email protocols. Many wireless networking standards, including WPA2 and WPA3, rely on AES for encrypting wireless communications. Furthermore, it's employed in secure messaging apps, digital rights management (DRM) systems, and hardware security modules (HSMs).
Key Facts
- Category
- technology
- Type
- technology